#11: Unlocking the Potential of ZK Proofs 🔓
Newsletter Content:
📰 Main Topic: Zero Knowledge Proofs
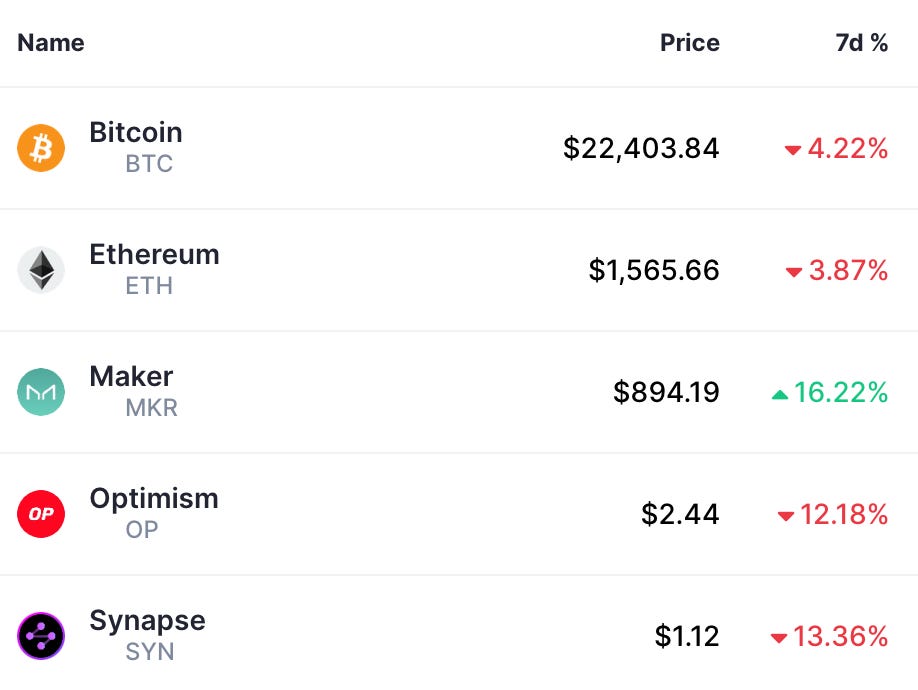
📈 Quote + Weekly Price Recap: See Below
🚨 Top Stories: Trouble for Silvergate / Bridge Reverse Exploit / EIP 4337 Deployed / Metamask x Unity Partnership / ETH Staking Withdrawal Upgrade Pushed Back
📖 Thread / Read of the Week: The Horse and the Farmer
📊 Visual of the Week: Comparing BTC Bear Markets
🔭 This Week: Calm Before the Storm
Imagine that you have buried treasure in a secret location, and you want to prove to your friend that you know where it is without actually revealing the location. You could use a ZK (zero-knowledge) proof to do this.
Here's how it would work:
You and your friend agree on a set of clues that will lead to the treasure's location. These clues are things like landmarks, secret symbols, or riddles.
Your friend then goes off to search for the treasure, armed with these clues.
When your friend thinks they have found the treasure, they send you a message with a secret code that is written on the treasure.
You then use the code to confirm whether or not your friend has actually found the treasure.
The key here is that you didn't reveal the location of the treasure itself, but you were still able to prove that you knew where it was located.
This is similar to how zero-knowledge proofs work in cryptography: they allow one party to prove to another that they know something (like a password or private key) without revealing the actual information itself.
Why is this so powerful?
Privacy / Security: Given that data breaches increase every year, users shouldn't need to include a robust dataset of information about themselves on every website they want to create an account on.
Less websites with my information = less places for my data to be stolen.Supply chain: A company could use a ZKP to prove that a particular bottle of wine was produced in a specific region without revealing any information about the production process.
Password Authentication: ZKPs can be used to verify a user's password without transmitting the actual password over the network, thus reducing the risk of password theft.
Digital Identity Verification: ZKPs can be used to verify an individual's identity without the need for sharing any personal information such as their name, date of birth, or social security number. This can be useful in situations where identity verification is required, such as opening a bank account or applying for a loan.
Quote of the Week:
“An investment in knowledge pays the best interest." - Benjamin Franklin.
Price Performance:
Top Stories:
Silvergate in Trouble: Partners Leave Board, Shares Drop Sharply (Blockonomi)
Liquidity issues at a bank… a tale as old as time. Silvergate was the primary bank that helped 1,600+ institutions access on and off ramps for digital assets for their customers.
Silvergate and its liquidity problems have been watched closely since the fall of FTX, with Silvergate (SI) losing $8B of deposits (withdrawn, not like FTX lost) and reporting a $1B loss for Q4 of last year.
Things recently went from bad to worse as they delayed their annual financials and expressed concern about their future. This was quickly followed by announcements from large customers deciding to cut ties with the bank.
Some of the notable companies who let Silvergate go:
Coinbase
Gemini
Paxos
Galaxy Digital
Circle
The amount of touch points that Silvergate has within the crypto sector can not be understated. This will be an important situation to monitor.
Wormhole Bridge: Reverse Exploit
Cross Chain bridges are the most sought after paydays for any hacker.
Why?
Think of a bridge like a foreign currency exchange. There are currencies being exchanged at all times, and the facilitator of those deals earns a commission. Therefore, these bridges store massive amounts of digital assets on their platform.
In February 2022 a hacker stole 120k ETH (hundreds of millions of USD) from the Wormhole bridge. With a $10M bounty in place, white-hat hackers (ethically sound hackers that spot vulnerabilities in digital infrastructure) found an exploit in the hackers processes.
While it is extremely positive that stolen funds have been recovered, the reason they were able to be recovered has raised some concerns across DeFi.
Essentially, the smart contract that stolen funds were deposited into was an upgradable contract, meaning it could be changed or improved by the owner(s). Like a democracy, changes to a smart contract require a vote from respective stakeholders. However, in this case the change was from a court order from the High Court of England.
Doesn’t seem so “decentralized” to me…
Note that while the hacker was able to steal the funds from the bridge, the fully transparent nature of the blockchain allowed investigators to follow the trail of money in real time and execute this “reverse-hack”. It is a huge misconception that crypto is often used for illegal activity and money laundering, as people don’t realize it is near impossible to convert illicit crypto into “real cash” when you want to spend it.
EIP-4337 Deployed:
A huge steps towards adoption, broken down extremely well by someone I have followed for a while.
EIP = Ethereum Improvement Proposal
Shanghai ETH Upgrade Pushed Back to April (DeCrypt)
Three things are certain in life:
Death
Taxes
Delayed Upgrades to Ethereum’s Network
Metamask x Unity SDK:
Many people see Web3 gaming as one of the subdivisions of crypto that can appeal to the masses. Here is a great breakdown of this recent partnership:
Thread / Read(s) of the Week:

Visual of the Week:
This Week:
Tuesday (3/7): Powell Speaks to Senate
Wednesday (3/8): JOLTS Job Report
Friday (3/10): February Jobs Report